More
- Topic1/3
16k Popularity
9k Popularity
16k Popularity
7k Popularity
2k Popularity
- Pin
- 🎊 ETH Deposit & Trading Carnival Kicks Off!
Join the Trading Volume & Net Deposit Leaderboards to win from a 20 ETH prize pool
🚀 Climb the ranks and claim your ETH reward: https://www.gate.com/campaigns/site/200
💥 Tiered Prize Pool – Higher total volume unlocks bigger rewards
Learn more: https://www.gate.com/announcements/article/46166
- 📢 ETH Heading for $4800? Have Your Say! Show Off on Gate Square & Win 0.1 ETH!
The next bull market prophet could be you! Want your insights to hit the Square trending list and earn ETH rewards? Now’s your chance!
💰 0.1 ETH to be shared between 5 top Square posts + 5 top X (Twitter) posts by views!
🎮 How to Join – Zero Barriers, ETH Up for Grabs!
1.Join the Hot Topic Debate!
Post in Gate Square or under ETH chart with #ETH Hits 4800# and #ETH# . Share your thoughts on:
Can ETH break $4800?
Why are you bullish on ETH?
What's your ETH holding strategy?
Will ETH lead the next bull run?
Or any o
- 🧠 #GateGiveaway# - Crypto Math Challenge!
💰 $10 Futures Voucher * 4 winners
To join:
1️⃣ Follow Gate_Square
2️⃣ Like this post
3️⃣ Drop your answer in the comments
📅 Ends at 4:00 AM July 22 (UTC)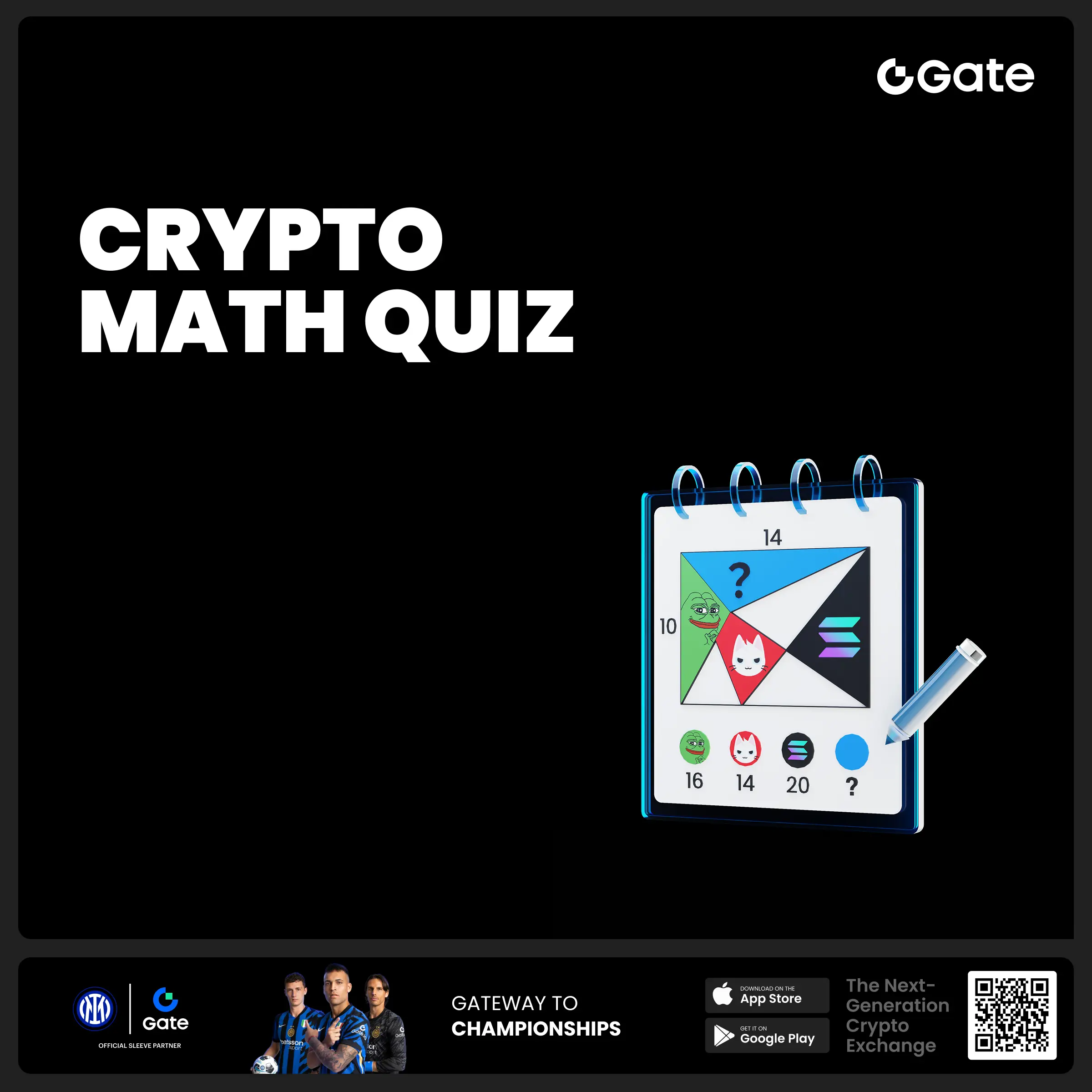
- 🎉 [Gate 30 Million Milestone] Share Your Gate Moment & Win Exclusive Gifts!
Gate has surpassed 30M users worldwide — not just a number, but a journey we've built together.
Remember the thrill of opening your first account, or the Gate merch that’s been part of your daily life?
📸 Join the #MyGateMoment# campaign!
Share your story on Gate Square, and embrace the next 30 million together!
✅ How to Participate:
1️⃣ Post a photo or video with Gate elements
2️⃣ Add #MyGateMoment# and share your story, wishes, or thoughts
3️⃣ Share your post on Twitter (X) — top 10 views will get extra rewards!
👉
Record $1.46 billion stolen: Analysis and insights on the major security incident of Cold Wallets
Analysis of the Large-Scale Fund Theft Incident Involving Bybit Cold Wallet
On February 21, 2025, a well-known trading platform's Ethereum Cold Wallet encountered a serious security incident, resulting in a loss of approximately $1.46 billion in assets, making it one of the largest security incidents in Web 3.0 history.
Event Overview
At UTC time 14:16:11 on the same day, the attacker successfully induced the Cold Wallet signer to sign a malicious transaction through a carefully designed phishing attack. This transaction was disguised as a routine operation, but in reality, it replaced the implementation contract of the Safe multi-signature Wallet with a malicious contract containing backdoors. The attacker then exploited this backdoor to transfer a large amount of assets from the Wallet.
Attack Details
Attack Preparation: The attacker deployed two malicious contracts three days in advance, which included a funding transfer backdoor and the ability to modify storage slots.
Signature Fraud: The attacker successfully deceived all three owners of the multi-signature Wallet into signing a transaction that appeared normal but was actually malicious.
Contract Upgrade: By executing the deleGatecall operation, the attacker changes the implementation contract address (masterCopy) of Safe to a malicious contract address.
Fund Theft: Using the upgraded malicious contract's sweepETH() and sweepERC20() functions, the attacker transferred all assets from the Cold Wallet.
Vulnerability Analysis
The core vulnerability of this incident lies in a successful social engineering attack. The attacker, through a carefully designed interface, made the transaction appear as a normal operation on Safe{Wallet}, while the data sent to the Cold Wallet had been tampered with. The signer did not verify the transaction details again on the hardware device, ultimately leading to the success of the attack.
Analysis indicates that this attack may have been planned and executed by a well-known hacking organization, and its methods are similar to recent incidents involving high-value asset theft.
Lessons Learned
Strengthen device security: Implement strict endpoint security policies, using dedicated signing devices and temporary operating systems.
Enhance security awareness: Conduct regular phishing attack simulations and red team defense exercises.
Avoid Blind Signing: Carefully verify the details of each transaction on the hardware Wallet.
Multi-verification: Use transaction simulation and dual device verification mechanism.
Be vigilant for anomalies: immediately terminate the transaction and initiate an investigation upon discovering any anomalies.
This incident once again highlights the security challenges faced in the Web3.0 space, particularly the systemic attacks targeting high-value targets. As attack methods continue to evolve, trading platforms and Web3.0 institutions need to comprehensively enhance their security measures to cope with increasingly complex external threats.