- Topic1/3
12k Popularity
61k Popularity
14k Popularity
20k Popularity
2k Popularity
- Pin
- #Gate 2025 Semi-Year Community Gala# voting is in progress! 🔥
Gate Square TOP 40 Creator Leaderboard is out
🙌 Vote to support your favorite creators: www.gate.com/activities/community-vote
Earn Votes by completing daily [Square] tasks. 30 delivered Votes = 1 lucky draw chance!
🎁 Win prizes like iPhone 16 Pro Max, Golden Bull Sculpture, Futures Voucher, and hot tokens.
The more you support, the higher your chances!
Vote to support creators now and win big!
https://www.gate.com/announcements/article/45974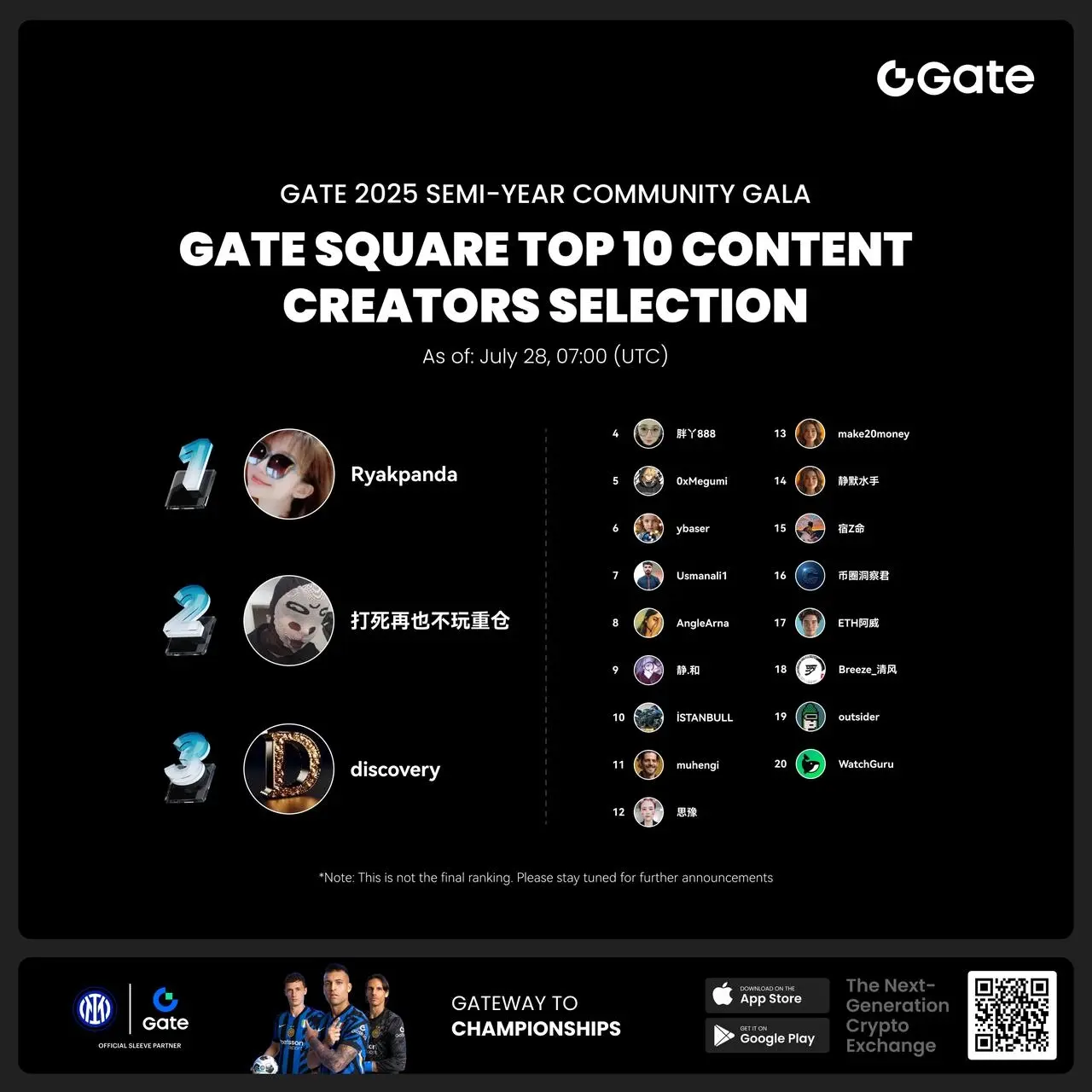
- 🎉 Hey Gate Square friends! Non-stop perks and endless excitement—our hottest posting reward events are ongoing now! The more you post, the more you win. Don’t miss your exclusive goodies! 🚀
1️⃣ #ETH Hits 4800# | Market Analysis & Prediction: Boldly share your ETH predictions to showcase your insights! 10 lucky users will split a 0.1 ETH prize!
Details 👉 https://www.gate.com/post/status/12322612
2️⃣ #Creator Campaign Phase 2# |ZKWASM Topic: Share original content about ZKWASM or its trading activity on X or Gate Square to win a share of 4,000 ZKWASM!
Details 👉 https://www.gate.com/post/st
V2EX users expose a recruitment project hiding malicious code, suspected of stealing Crypto Assets.
PANews, July 28 news, according to V2EX website, user evada recently posted that during the job application process, they were required to use a GitHub project template specified by the recruiting party to develop the page, and found that the project contained malicious code. Specifically, the logo.png file in the project appears to be an image, but actually contains executable code, which is triggered for execution through the config-overrides.js file, with the intent to steal the user's local Crypto Assets Private Key. Evada pointed out that the malicious code sends requests to specific URLs, downloads trojan files, and sets them to start automatically on boot, exhibiting a high level of concealment and harm. V2EX administrator Livid stated that the involved accounts have been banned, and GitHub has also deleted the related malicious repositories. Several users commented that this type of new scam targeting programmers is highly deceptive, reminding developers to be vigilant when running projects from unknown sources.